In my studies of social psychology, there are two behaviors that pop up frequently. This would be especially true as it relates to a discussion about security. These are the two extreme behaviors. Also, it should be noted that these behaviors do not present themselves as frequently when dealing with professionals who deal with security issues on a daily basis. In other words, these are two extreme behaviors that occur with “security newbies.”
A Brief Look at Some Personality Types
It may seem silly to talk psychology, but it does relate to how people respond to information that they receive. It also relates to how people may avoid receiving needed information that will help keep them safe.
The Ignore-It-Until-Later Personality
For the Ignore-It-Until-Later Personality, the first response is to ignore it. The people who ignore the topic of security are the ones who are likely to say, “Oh, what article? No. I didn’t see it.” They may also go so far as to say they don’t need security for their site. They have it covered because they are using XYZ WordPress plugin. Or, they have it covered because they have someone “on it,” whether that is a person they have hired, their spouse, or the company where they host the site. These individuals may not even realize that they are ignoring the topic of security or putting it off for a later time. It is simply a part of their personality and approach to life.
Before we fault them, we have to realize that we all do it, to some extent. Those things that are not our forte fall a little lower on the list. For example, when was the last time you got an oil change for your car? How about exercise – how is that going? And, the list could go on and on for any of us, eh?
The-Sky-Is-Falling Personality
The other personality type is the one who sees a conspiracy around every corner and is sure that it is coming their way. There may be some truth to what they are thinking, but the balance may be a bit off and maybe that conspiracy is after their neighbor and not them (just kidding). These types of people recognize the concern for security, and they may even be implementing steps to ensure that they are secure, but sometimes the fear factor gets the better of them, and they are either missing the appropriate steps or “over-doing it.”
The Balanced View (the Goal)
This balanced view is the result that we seek. We need to be informed (to ensure our personal and professional security), but we also need to find an approach that is calm and strategic. Now, let’s look at information that we need to reach that goal. To give you a hint, we will be talking about adding a virtual private network and content delivery network to your personal and professional strategy for efficiency, performance, and security.
VPN: Start with Your Home or Office
A virtual private network (a.k.a. VPN) is like an encapsulated network just for you, or just for your company. Ok, honestly, the word “private” is much easier to understand than a work like “encapsulated.”
Let’s take a step back and look at the World Wide Web, otherwise known as the Internet. It is a global network where people are connected from everywhere or anywhere. The idea of a VPN is to create a smaller version of that that also connects back to the World Wide Web as a sort of grouping (network).
Sometimes it is easier to understand what a VPN is by looking at the purpose(s) of the VPN. The two key purposes are security and privacy. Let’s look at these in more depth.
Security
By having a virtual security wall, a firewall, you can protect your identity, profile information, location identification, and IP address. One way that this protection is accomplished is by securing your Wi-Fi. Since many of us use a Wi-Fi set-up at home, this is essential. More and more offices are also using Wi-Fi in a corporate environment. If it isn’t the main method of local area network (and a World Wide Web connection), it is many times the backup solution in those work environments. A VPN provides the opportunity to secure that connection and protect it (and your identity) from the outside world.
Another security aspect that affects Wi-Fi is accessibility to Hackers. If you are using a free Wi-Fi, your system is vulnerable to the online identity thieves, as they grab the info through the insecure method of your connection to the Internet. This is another area where the properly selected and configured VPN can protect you.
Privacy
In the same way that the VPN provides the security, it also uses the same technology to protect your privacy. This protection is important if you would prefer that hackers not have access to what you are doing and where you are doing it. For those who wish to keep their location private, the VPN is a part of the solution to ensure that their location is known only to them.
Some performance concerns that may come to mind might include speed and ease of use. If you have reached the point of deciding that your security and privacy matter enough that you need a VPN, your next questions may include those performance and functionality questions. That is where you will want to come up with a list of what is important to you and check out the VPN services to see if they address your additional issues. For example, in the case of hide.me (inspiration for the list of suggested features for a virtual private network provider), they suggest that their service is easy-to-use (or easier-to-use) and also grants you the speed that you want. These are examples of two items that should be on your list when making that decision. You can visit their site to see other items that extend the VPN service beyond the coverage of security and privacy (like Global TV benefits that are made possible through the use of the VPN).
CND: Secure Your Site
We all want security. Right? We just covered our personal security, and now we are moving on to the security of our website. These days, most businesses (and even private individuals) have websites.
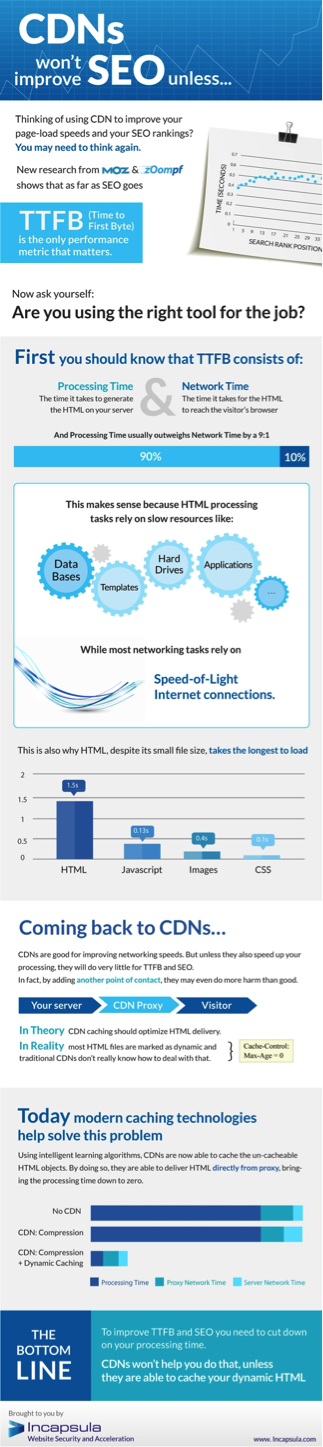
What is a Content Delivery Network?
A content delivery network (a.k.a. Content Distribution Network; CDN) serves many purposes and addresses/solves many issues. One such concern that is often overlooked by those who are new to the concept of CDNs is “hack proofing” the site. In other words, protecting your site against hacking. Gail Gardner, a small business strategist, has written an excellent article on the topic, “Your Site IS Under Attack! Use a CDN to Keep Out Hackers, Scrapers, and Bots.” If you are new to the topic, you will want to visit that article and read up on the concern(s), as well as the solution. Don’t forget to share it with your friends.
The Basic Functionality of Properly Configured CDNs
First, let’s talk about caching. The CDN caches a copy of your site. Have you ever visited a site and found that even when the electricity goes off, you are still able to see the site in your browser? This happens for two reasons. One reason would be that the site was already in your browser tab when the electricity went out, and you never closed it or reloaded/refreshed. The other reason is that the browser cached the web page, and it is now stored on your computer. Another term for this case (in Microsoft terms) is “temporary internet files.” In the same way, a CDN stores versions of your web pages and website on their server.
Some of what CDNs help you accomplish covers the area of performance. For example, CDNs help to reduce the size of the images, and reduce the number of connections (especially dormant connections) to your server (leaving more resources for additional connections). The properly configured CNS also caches the site and is able to determine what type of application (i.e. static; dynamic) is needed so as to cache the content in the most efficient manner.
Protecting Your Site Against the Intrusion
After signing up for your CDN, one of the first steps is configuring your site with that new CDN. When your site is properly configured, this is what happens in the context of the visitors’ experience: the visitors visit the site, and the site triggers the CDN to serve up the cached pages. This alleviates the load (bandwidth) on your main hosting server.
Why is that? Without a CDN, each page is retrieved from the host server as if it is a fresh request. Technically it is a fresh request. The host provider’s server doesn’t know the difference. It sees each request as a full, new request and takes the time to load up the page and serve it to the visitor.
Let’s say that the page dynamically loads your name, your address, and your pet’s name and color. Each time that someone visits your site, that page makes a call to the database (assuming a blog or dynamically loading page) and asks it what the name, address, and pet’s name is. After the database responds with that information, the dynamic page displays it.
What if that same visitor shuts down his computer and goes out for coffee. When he returns, he remembers that he wanted to know more about you and your site and re-visits that page. As soon as he hits the page, that same call is made to the database, requesting the information about you, your address, and your pet.
Does that make sense? Well, it does. Yes, and no. What makes the most sense is for the page to remember that it has been accessed and that it has provided that information. Let’s say that retrieving the information takes two minutes. Let’s say displaying information that it already has takes 10 seconds. Your visitor accessed the “information page” (i.e. about us) twice, for a total of four minutes. Even if the access of that information were the first time, for the first visit, it would only be two minutes 10 seconds if there were a properly configured CDN in place.
That is because the CDN stores that information and rather than involving the database, simply serves up the requested information. A savings of almost 50%, in the example provided.
That CDN path involves the visitor visiting the site > the site accessing the CDN > the CDN accessing the host server (as necessary) > the host server communicating with the CDN (as necessary) > the CDN delivering the page to the visitor. In cases where the host server is not needed (repeat visits to a particular page), the path is even more simplified: visitor > the site accessing the CDN > the CDN responding back to the site > the page delivered to the viewer.
Now that we have the path figured out in our heads you can see how the CDN has the opportunity to deliver data and pages more efficiently. This path also allows the CDN to protect you from bots and hackers. Similar to a VPN or a firewall, the CDN can be configured to watch for those bots and watch for “bad traffic” and block it from receiving the content that is requested.
Remember that path, above, and bypassing the host server when the pages are cached? In the same way, if you do not want bots to access the site, you can configure it in your CDN settings. In that case, the bot accesses the site, which connects to the CDN. The CDN recognizes that it is a bot and responds with a block against the bot’s access to data or content.
When it comes to site attacks, many people only think about the concerns that happen AFTER that attack (i.e. a DDOS attack). However, the best way to protect and secure your site is through a preventative strategy, which includes a CDN. This allows you to track what is happening on your site and discover ways to facilitate better usage and more efficient measures, as well as the security that is needed for your site (i.e. blocking bots, hackers, and DDOS which occurs through the use of bots).
Infographic designed and provided by Incapsula. More at https://www.incapsula.com/cdn-content-delivery-network/.
In Summary
We are looking at solutions for privacy for ourselves, personally. We are also looking at ways to lock down our sites, prevent bots that can cause DDOS, and blocking hackers. We discussed how security could be accomplished through the use of a VPN. The VPN acts as a layer of protection between yourself and the rest of the world.
Note: Keep in mind that there is no such thing as 100% protection. The only way that that is attained is to resist the urge to use the Internet, ever. What we are recommending here are ways to reduce the likelihood of having security issues.
Once you have secured your home or office, the next level of concern is your site. This is especially true in cases of blocking hackers and DDOS (through bot attacks). It is important that your site is protected from hackers and bots. Since your site is hosted on a separate server (not in your home), there needs to be a separate solution. Fortunately, a properly selected and configured CDN alleviates your concerns and protects your site.
Through the use of a properly selected and configured VPN and CDN, you are a long ways down the road of protecting yourself (and your site). You have been able to approach it in a balanced manner and still address the issues adequately. What are you waiting for now? ![]()