Biometrics and Identity Theft Prevention: How Can Technology Protect Our Interests?
It shouldn’t be a surprise for customers when new payment methods are released through smartphone integration for acquiring products or services. The reason behind the consistent seek of improvement for e-commerce services is nothing more but the mere reflection on how virtual world evolves, requiring further controls in what regards to protecting customer’s data.
Given the latest news on how hackers have found ways of fooling top-notch security technologies, we can ask ourselves: how can technology prevent those events from happening?
It All Starts with Login Credentials
One of the most common mistakes when talking about identity theft prevention starts with Social Media and public internet networks. Users, mistakenly, rely on just one email account for managing both personal and professional life, which opens the gates for hackers to not just take control of our social media profiles but also to access sensitive data as private emails, banking information or details like our home address, car model and license plate, etc.
The threat of leaving so many aspects of our lives exposed to cyber criminals answers to the nowadays common link between internet security breaches and “traditional” ways of crime like extortion or kidnapping.
First Countermeasures Against Cybercrimes
The essential step we need to take is to create a spare email address for all our online activity dedicated to entertainment. By this, we can group social media, forums, online gaming, gambling, etc. Avoid repeating passwords along the internet, and be careful – in case you are a public persona – to leave traces that can expose your true identity and lifestyle (hence the reason why celebrities and politicians are well-known victims of hackers).
Photo courtesy of Negative Space
Next, you need to start considering how to improve your passwords to make them safer against unwanted intromissions. All passwords should, at least, count with alphanumeric characters, upper and lower cases, plus special characters like *!_/ and many other, etc.
When Technology Gives a Helping Hand
Until 3-4 years ago, people only counted with the protection of passwords and firewalls for protecting their identity. It’s true that public organisations and banking entities were slowly introducing variated methods that granted users the possibility of stronger protection layers for their data; thus those methods were complicated, time-demanding and, under most scenarios, not efficient enough when a rapid action was needed.
Regardless of what some banks may consider, digital keys are a thing to be forgotten, since Biometrics are taking the first place in secure authentication methods.
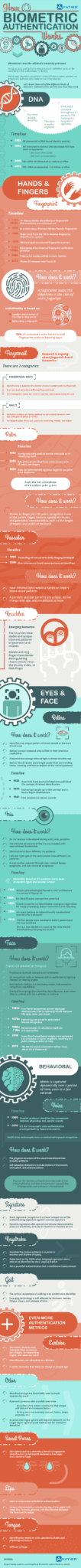
We can group under “biometrics” all those measurable parameters that craft a link between biological conditions and identity. For example, our fingerprints are unique, and no one else can have the same pattern as we do. By exploiting such biological elements, security industry was able to develop fingerprint readers which granted access to data (or physical locations) just to those whose fingerprints were registered in the database; and yet, it leaves a very precise physical trace as people can’t deny they accessed such place at a certain date and time.
Popular technologies that adapted the concept of biometrics are Apple’s TouchID, Samsung Iris Scan, Voice Recognition Software, Fingerprint Scanners, etc. For further references on this behalf, we can appreciate the topics covered in this infographic courtesy of Avatier.
Biometrics Guarantee Identity Fidelity
Unlike what spy movies tend to showcase, for the common user, there’s no possible way a hacker would take such much time and effort in replicating your biometrics. Therefore, it proves to be the most efficient method for identity verification.
Depending on the method used, there are some downsides we need to consider:
- Fingerprint access can be jeopardised if our fingers (or the device) are dirty, but also if we got any injury – superficial or a complicated outcome like breaking your wrist/fingers.
- Voice recognition may not be accurate depending on the fidelity of the recording method used the first time our voice tone was stored, but also due to conditions like catching a cold.
So far, the only biometrical factor that, unless a terrible accident happens, won’t be modified is the Iris Scan, as patterns in the ligaments of Iris’ muscles are created during gestation, and cannot change in adult life (unlike Iris colour that can suffer subtle changes due to a higher melanin concentration during the very early months of a child’s life). Therefore, if we seek for a way in which we can protect our data when login at certain services, this should be the preferred method for most people.
Keep in mind you are also reducing a risk factor by not login in public WiFi networks, as what would be the case of cybercafés, plazas, terminals or shopping malls. Identity Theft is a widely-spread crime these days, and it’s between our reach to prevent these inconveniences from happening to us.