How Vendor Management Secures Your Bank’s Customer Data
How many vendors can access your customer’s data? The answer might be more than you think.
Customer data flows through an intricate network of third, fourth, and even nth-party vendors. Data processors, call centers, marketing platforms, fintech partners, loan servicers — each connection multiplies your attack surface. When one link in this chain breaks, your customers pay the price.
Think about the 2023 ransomware attack on Infosys McCamish Systems, a back-office provider most consumers had never heard of. When that vendor was hit, personal data tied to customers at multiple financial institutions was exposed. Those institutions weren’t breached directly, but they still were held responsible for the breach as though their own systems had been attacked. It’s a reminder that a vendor you don’t control can still create a mess you have to clean up.
Some financial institutions weren’t using it themselves — but their vendors were. And in some cases, those vendors were. Banks learned about the connection only after sensitive customer data had already been swept up in the breach. It was a wake-up call: you can inherit risk from partners you didn’t even know you had.
In 2024, over a third of breaches were third-party related – a 6.5% increase from 2023. As third- and fourth-party breaches become increasingly common, it’s critical to protect your customers and their data.
A well-run vendor management program provides visibility into who accesses customer data and allows you to respond quickly when incidents occur. Let’s look at some key steps for a secure vendor management program.
Create a Vendor Inventory
Many financial institutions discover gaps in their vendor inventory only after a breach occurs. A vendor inventory is one of the first steps to securing customer data. You can’t manage what you’re not aware of. Your vendor inventory should include details like:
- The vendor’s product or service
- Risk level
- Criticality
- Type of data stored
- Critical fourth-party vendors
Keep this information in a centralized location that’s easily accessible to stakeholders. Regularly update the inventory to ensure you capture new technologies, expanded services, or new vendors.
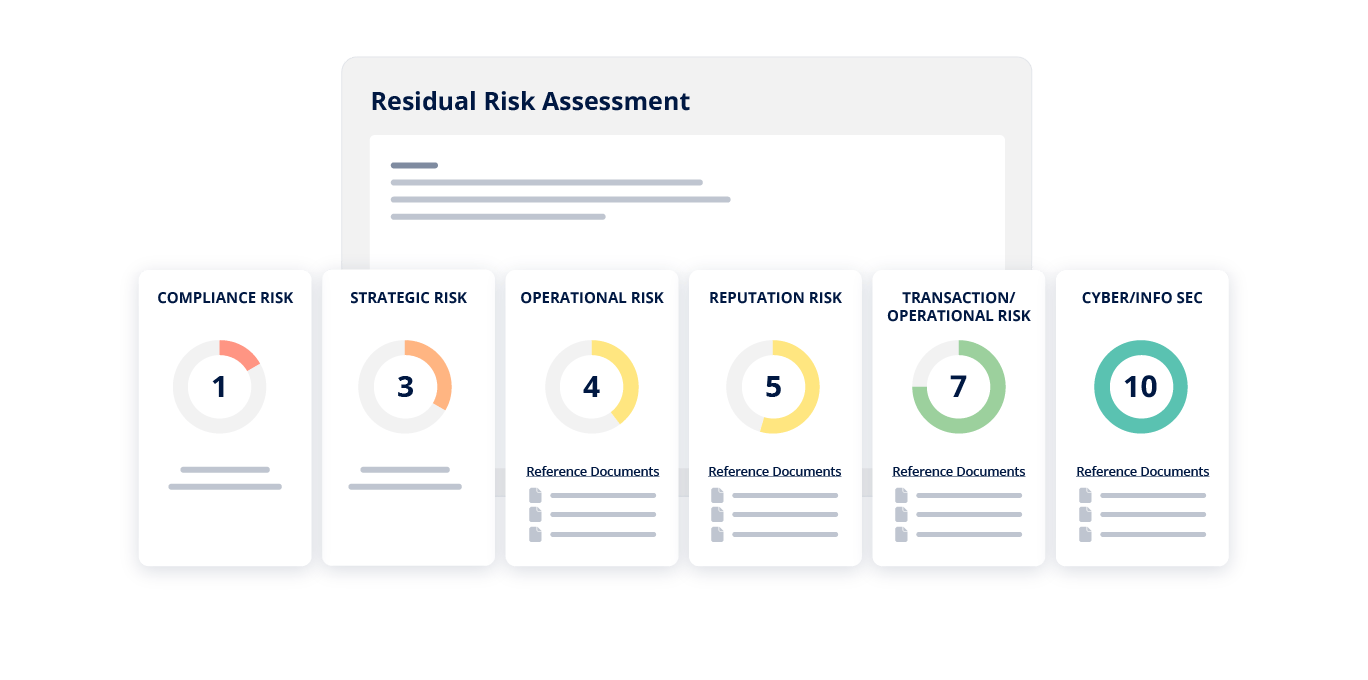
Assess Your Vendor’s Security Risk
A cloud storage provider handling sensitive financial records requires much more scrutiny than an office supply vendor. Start by categorizing vendors based on their access to customer data, system criticality, and regulatory scope.
High-risk vendors typically include those touching nonpublic personal information, core banking systems, or payment processing infrastructure. Review their cybersecurity frameworks, business continuity plans, incident response procedures, and relevant compliance certifications.
Look for red flags such as limited cybersecurity measures, lack of incident response plans, or poor financial health that could impact their ability to maintain security standards.
Collect Vendor Due Diligence
Risk assessments identify potential vulnerabilities, and due diligence proves whether vendors can actually protect your data. Request documentation that demonstrates security capabilities, including:
- SOC 2 reports
- Penetration testing results
- Security policies
- Cyber insurance certificates
- Business continuity plans
For vendors handling sensitive data, examine their encryption standards, access control mechanisms, employee background check processes, and data retention policies. These details reveal how vendors protect information from both external threats and insider risks.
When vendors can’t provide adequate documentation, that’s a signal to either work with them on remediation or reconsider the relationship entirely.
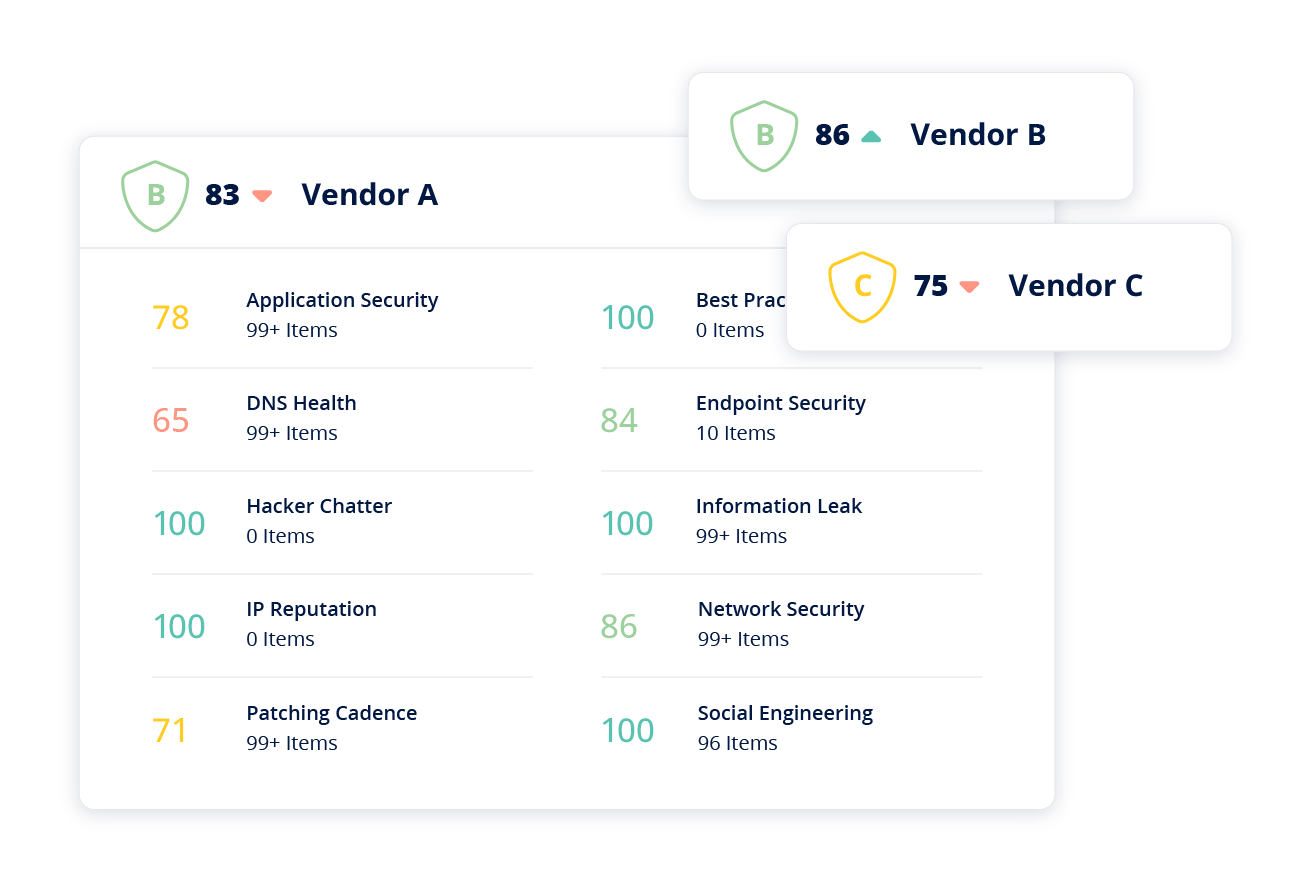
Continuously Monitor Vendor Cyber Risk
A vendor with strong security controls today could become vulnerable tomorrow through new threats, system changes, or degrading security practices. Continuous monitoring helps you spot problems before they become breaches.
Set up alerts for significant changes like leadership turnover, financial distress, or publicly reported security incidents. Many institutions now use threat intelligence feeds to track whether vendor domains appear in data leaks or are associated with malware. For your highest-risk vendors, establish regular touchpoints beyond annual reviews.
When a vendor experiences a security incident, even one that doesn’t directly impact your data, treat it as an opportunity to evaluate their response and determine if additional controls are needed.
Use Vendor Management Tools
Managing vendor relationships manually through spreadsheets becomes unmanageable as your vendor network grows. Vendor management tools centralize your inventory, automate due diligence collection, and track remediation efforts in one location.
These tools can automatically send assessment questionnaires, flag expired documentation, and provide risk scoring across your entire vendor portfolio. The right software vendor, like Ncontracts help you make faster, more informed decisions about vendor relationships and demonstrate regulatory compliance when examiners come calling.
Conclusion
Third-party breaches won’t disappear, but a strong vendor management program significantly reduces your exposure. Each layer, from risk assessments, due diligence, and continuous monitoring, builds your defenses.
Your customers trust you with their most sensitive information – effective vendor management helps you honor that trust.
This article has been published in accordance with Socialnomics‘ disclosure policy.